Assessing Cyber Risk in Your Suppliers: Why & How to Transform Your Practices

The growing dependence of companies on vast, interconnected digital ecosystems is radically reshaping how cyber risk must be approached. The 2025 edition of the TPRM Observatory, conducted by Board of Cyber and CESIN, confirms a now-central trend: cyber risk from suppliers is no longer peripheral — it has become strategic, and is now recognized as a systemic risk by most organizations. Yet despite this awareness, current assessment methods remain largely suboptimal and insufficiently industrialized.
Context: Cybersecurity & TPRM as Structural Challenges
The generalization of digital services, outsourcing of processes, and technological standardization have significantly widened the attack surface of organizations. According to the Observatory, 81.8% of companies consider third-party risk to be important or very important TPRM Observatory 2025 _ CESIN …
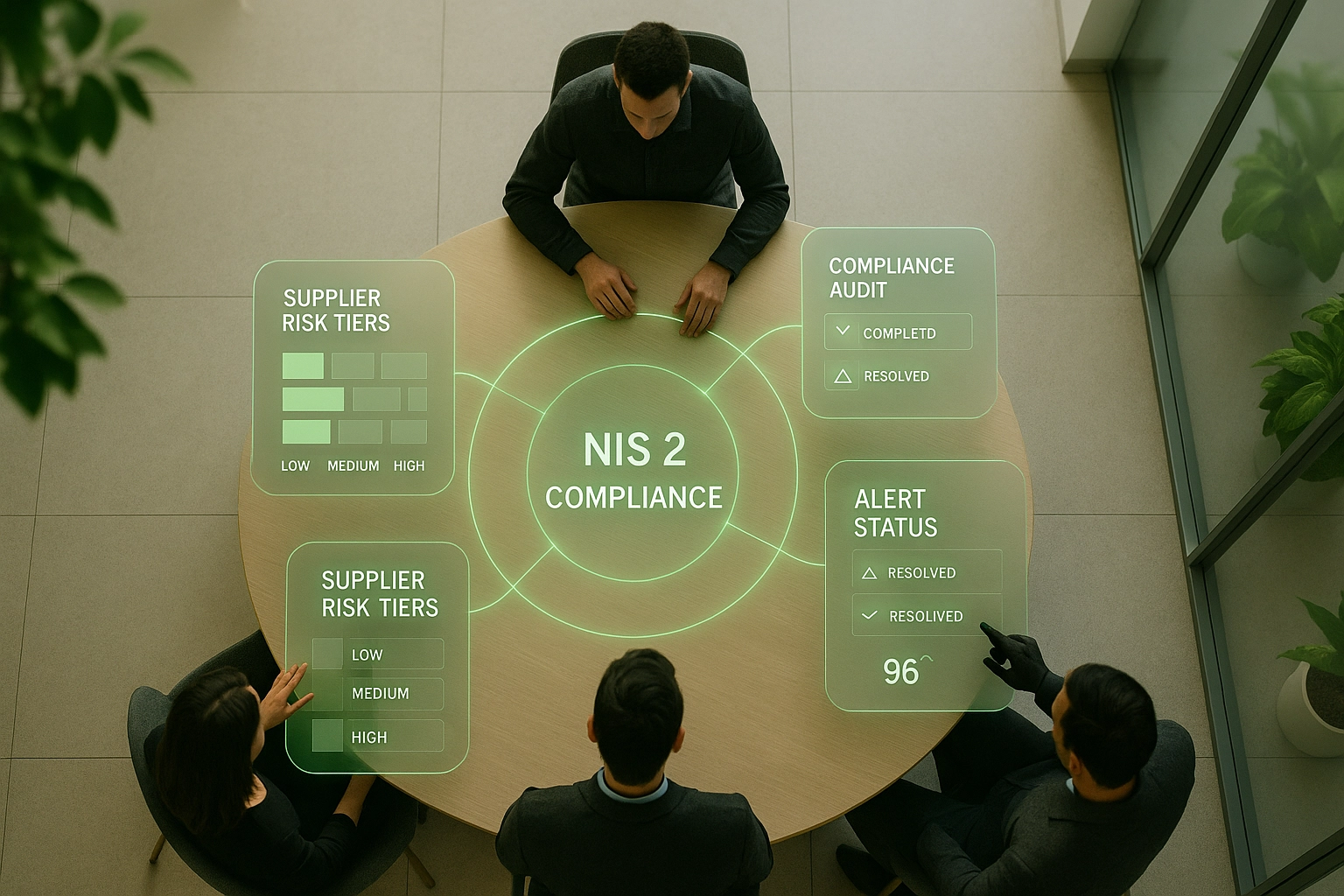
At the same time, regulatory pressure is intensifying: NIS2, DORA, the AI Act… These frameworks demand stronger security and control standards.
This growing maturity is reflected in more structured governance: 60% of companies now centralize third-party risk management, and 54% elevate the topic to the executive committee level TPRM Observatory 2025 _ CESIN …
As a result, supplier cybersecurity is no longer just a technical topic — it’s a governance and resilience issue that involves the entire organization.
New Personas, But Still Limited Methods
The study highlights the emergence of new personas involved in TPRM: beyond CISOs, legal departments, procurement, compliance, and business functions are increasingly engaged. This diversity reflects a desire to address supplier cyber risk in a cross-functional way.
However, despite this mobilization, assessment methods remain overly focused on self-declared questionnaires — tools that are seen as time-consuming, unreliable, and hard to scale.
According to the Observatory:
- 60% of companies still use security questionnaires (declining, but still the majority)
- 75% use a Security Assurance Plan (PAS)
- More objective approaches — SOC 2 certification, audits, external ratings — are on the rise but still a minority TPRM Observatory 2025 _ CESIN …
This paradox illustrates a growing maturity that is still held back by its tools.
The Four Key Challenges of Supplier Cyber Risk Assessment
Surveyed companies consistently point to recurring roadblocks. The 2025 Observatory identifies four major obstacles:
1. Lack of Human & Financial Resources
68% of organizations report lacking the resources to conduct necessary assessments. This structural limitation prevents large-scale supplier risk management.
2. Difficulty Engaging Suppliers
64% struggle to get complete, reliable, or timely responses. Some partners — particularly major cloud providers — even refuse audits or questionnaires altogether.
3. Uneven Maturity Among Third Parties
52% of companies find that their suppliers fail to meet expected security levels. The supply chain remains highly vulnerable.
4. Scaling Issues & Lack of Mutualization
41% cite the inability to industrialize their processes.
And 31% lament the absence of shared platforms to avoid redundant audits TPRM Observatory 2025 _ CESIN …
These insights confirm the urgent need for a new model: supplier assessments can no longer rely on manual campaigns or the goodwill of third parties.
When & How to Identify Your Suppliers’ Cyber Risks
The Observatory reveals that 63% of companies assess fewer than 50 suppliers per year, even though they may have hundreds or thousands. This lack of scrutiny often stems from the limitations of their methodology, which can’t effectively process questionnaire responses — assuming they even get responses.
Yet cyber risk should be assessed at three critical moments:
1. During Supplier Onboarding
Evaluate service criticality, data access, and system integration level.
68% of companies now classify suppliers by risk — a sharp increase TPRM Observatory 2025 _ CESIN
2. Before Contract Signing
Include security clauses, certification requirements, and audit rights.
For 9 out of 10 companies, the contract remains the main governance tool.
3. Continuously Throughout the Relationship
Risks evolve over time: vulnerabilities, incidents, data breaches, infrastructure changes.
Yet today, only a minority of organizations monitor third-party exposure continuously.
The challenge: moving from one-time evaluations to dynamic, ongoing monitoring.
Solution: Automation & Mutualization — The Future of Supplier Cyber Assessment
The Observatory’s conclusion is clear: 80% of companies are open to mutualizing supplier assessments, and 77% want to rely more on recognized certifications (ISO, SOC 2, etc.) to reduce questionnaire use.
Two key trends are emerging:
1. Automating Controls
CISOs express strong demand for tools that can:
- Automatically collect evidence
- Continuously assess security posture
- Generate alerts in case of drift
- Reduce operational workload from questionnaires
- Automate evaluations
This automation is becoming essential to scale up operations.

2. Mutualizing Assessments: A Future-Proof Model
The study shows strong support for a shared model based on:
- Common risk frameworks
- Reusable third-party evaluations
- Mutual recognition of certifications
- A trusted institutional environment
As one CISO put it:
“Mutualization is the only viable alternative to an inefficient, time-consuming system that relies too heavily on self-filled questionnaires that serve as little more than a formality.” TPRM Observatory 2025 _ CESIN …
Move to proactive risk management today!
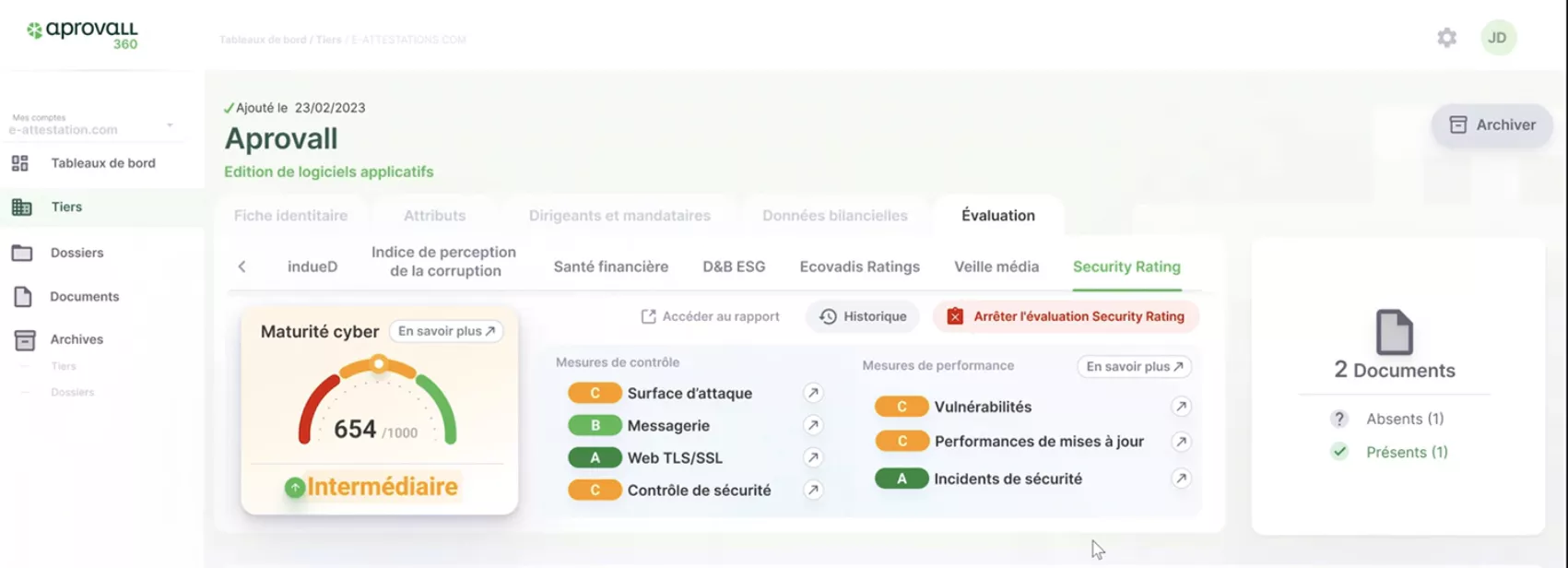
With Aprovall360, benefit from an intuitive and powerful solution designed to meet the requirements of the most highly regulated industries. Don’t just react to risks — anticipate them, measure them, and manage them with confidence.
These articles might interest you
-
 14 July 2024Duty of vigilance: A recent international report warns of companies’ non-compliance, particularly in FranceSolutionsThe World Benchmarking Alliancehas just published a report analyzing the practices of the 2,000 most important companies on the planet in terms of human rights due diligence. The “alarming” results show companies’ delay in this area, and French companies are far from being an exception to the rule. The countdown has begun before the European […]
14 July 2024Duty of vigilance: A recent international report warns of companies’ non-compliance, particularly in FranceSolutionsThe World Benchmarking Alliancehas just published a report analyzing the practices of the 2,000 most important companies on the planet in terms of human rights due diligence. The “alarming” results show companies’ delay in this area, and French companies are far from being an exception to the rule. The countdown has begun before the European […]Read more
-
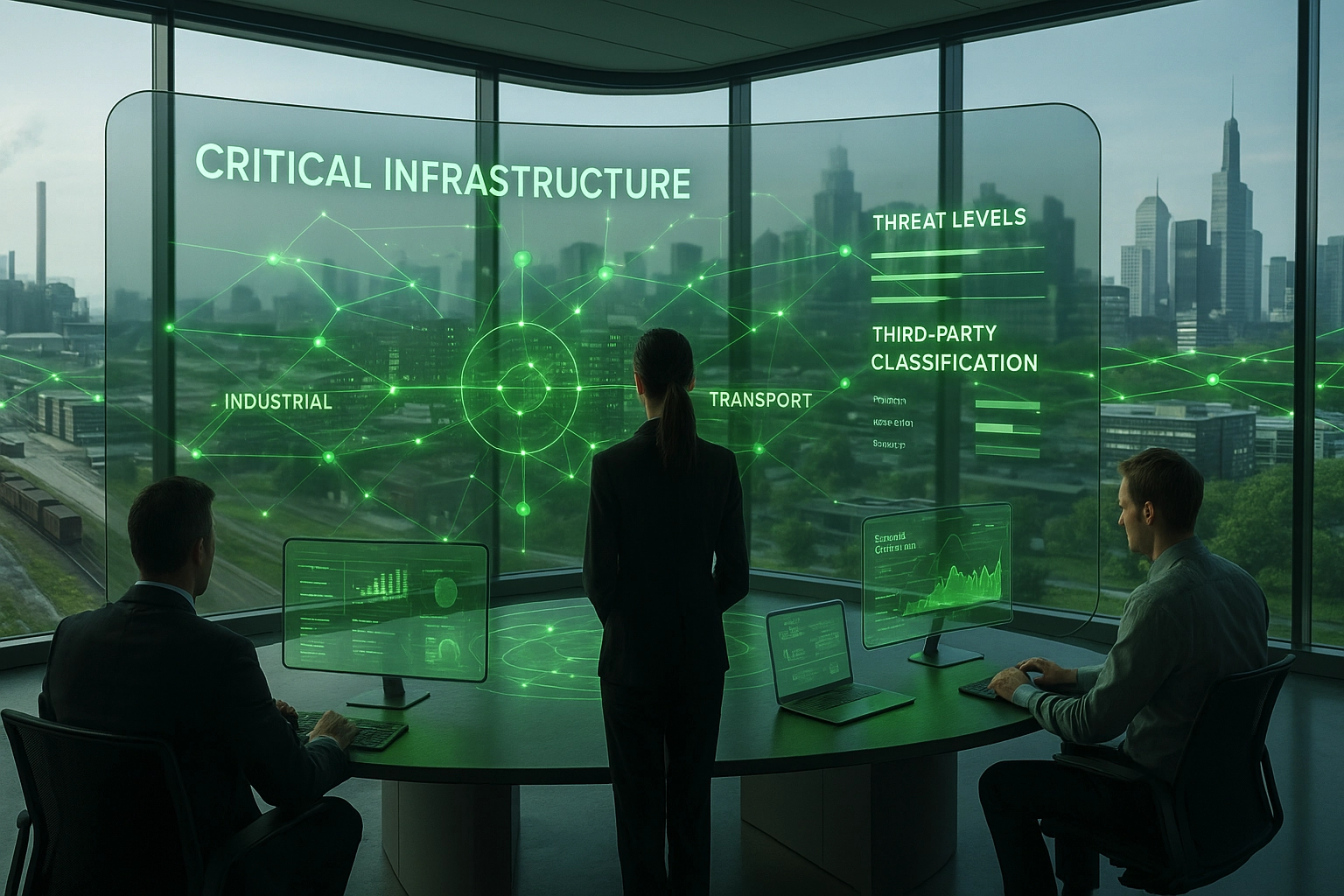
 21 April 2025NIS2: Understanding the Obligations of Critical SuppliersSolutionsThe NIS2 Directive redefines cybersecurity requirements for critical entities and their third-party governance across Europe. With over 1.8 million companies indirectly affected via their supply chains (NIS2 Quality Mark – 2025), identifying critical third parties is now a strategic imperative for key sectors like construction and public services. This regulation mandates a dynamic mapping of […]
21 April 2025NIS2: Understanding the Obligations of Critical SuppliersSolutionsThe NIS2 Directive redefines cybersecurity requirements for critical entities and their third-party governance across Europe. With over 1.8 million companies indirectly affected via their supply chains (NIS2 Quality Mark – 2025), identifying critical third parties is now a strategic imperative for key sectors like construction and public services. This regulation mandates a dynamic mapping of […]Read more
-
 11 February 2025NIS 2 Directive and Critical Third Parties: A Must-Read Guide for CompaniesSolutionsIdentifying and evaluating critical third parties is becoming a key challenge with the NIS 2 Directive, which is reshaping strategic partner governance across Europe. This regulatory shift, affecting approximately 300,000 institutions, redefines collaborative evaluation requirements for third parties in critical sectors such as construction, industry, retail, and the public sector. At the heart of this transformation […]
11 February 2025NIS 2 Directive and Critical Third Parties: A Must-Read Guide for CompaniesSolutionsIdentifying and evaluating critical third parties is becoming a key challenge with the NIS 2 Directive, which is reshaping strategic partner governance across Europe. This regulatory shift, affecting approximately 300,000 institutions, redefines collaborative evaluation requirements for third parties in critical sectors such as construction, industry, retail, and the public sector. At the heart of this transformation […]Read more
-
 19 March 2025Digital Transformation and Third-Party Governance: A New Era for Risk ManagementSolutionsDigital transformation is profoundly redefining the way organizations manage their relationships with third-party partners. In this rapidly evolving context, third-party governance is taking on a crucial strategic role, moving from simple document collection to collaborative compliance assessment. This shift is part of a broader movement toward Third Party Governance and Risk & Compliance (TPGRC), which […]
19 March 2025Digital Transformation and Third-Party Governance: A New Era for Risk ManagementSolutionsDigital transformation is profoundly redefining the way organizations manage their relationships with third-party partners. In this rapidly evolving context, third-party governance is taking on a crucial strategic role, moving from simple document collection to collaborative compliance assessment. This shift is part of a broader movement toward Third Party Governance and Risk & Compliance (TPGRC), which […]Read more